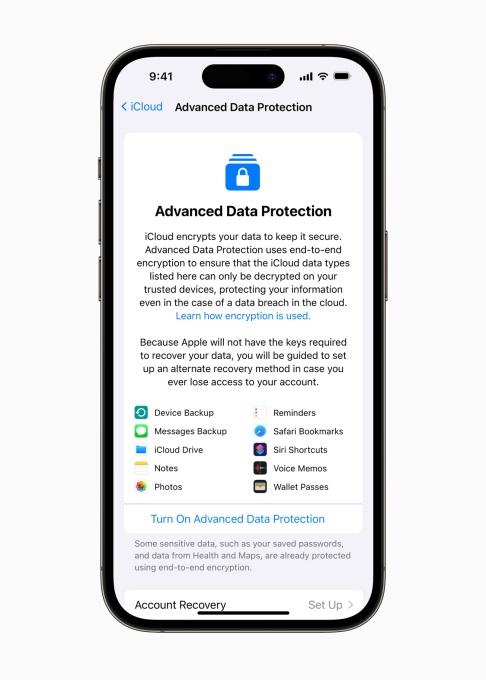
Apple today launched Advanced Data Protection, a new, optional end-to-end encryption scheme that prevents data in a customer’s iCloud from being decrypted on an “untrusted” device. Concretely, Advanced Data Protection would keep most of an iCloud account’s data secure even in the event that Apple was hacked, and — as a Wall Street Journal piece notes — would prevent Apple from accessing iCloud phone backups in response to law enforcement requests.
Currently available in the U.S. for members of the Apple Beta Software Program and coming to all U.S. users by the end of the year (with the rest of the world to follow in 2023), Advanced Data Protection gives iCloud users’ trusted devices (e.g. iPhones and Macs) sole access to the encryption keys for the bulk of their data. (For the uninitiated, encryption keys are the random strings of bits specifically generated to scramble and unscramble data.) Once the feature is enabled, Apple servers can’t modify certain iCloud settings on behalf of users or access data stored in iCloud backups, Photos, Notes and CloudKit fields that third-party developers opt to mark as encrypted.
Prior to the rollout of Advanced Data Protection, iCloud users couldn’t prevent Apple from pouring through the contents of device backups, including text messages and contacts, if it chose to do so. Readers might recall the tech giant’s fight with the FBI over the San Bernadino shooter’s encrypted iPhone data, during which the agency attempted to force Apple through the courts to unlock a protected iPhone. At the time, Apple argued that the FBI could instead access the data it sought via the unencrypted iCloud backups on its servers.
Image Credits: Apple
Notably, Advanced Data Protection doesn’t work with iWork collaboration tools, Shared Albums in Photos, iCloud Mail, Contacts or Calendar; Apple blames the interoperability requirements. And to enable the feature, users must enroll in two-factor authentication for their Apple ID and set a password or passcode on their devices, as well as update those devices to the newest available software (iOS 16.2, iPadOS 16.2, macOS 13.1, tvOS 16.2, watchOS 9.2 and the latest version of iCloud for Windows).
Advanced Data Protection doesn’t yet support managed Apple IDs and child accounts, Apple clarifies in a support document.
A word to the wise, the penalty for failing to set a recovery method for Advanced Data Protection is quite steep. Apple notes that if the recovery fails — for instance, if a recovery contact’s information is out of date — any encrypted iCloud data is as good as lost.
Alongside Advanced Data Protection, Apple this morning announced two other security-related capabilities coming to its product ecosystem: iMessage Contact Key Verification and Security Keys.
iMessage Contact Key Verification allows users “who face extraordinary digital threats,” such as journalists and members of government, to choose to further verify that they’re messaging only with people they intend. Apple says that iMessage Contact Key Verification will send an alert if an adversary breaches cloud servers to eavesdrop on encrypted communications and allow users to compare a special ID-verifying contact verification code in person, on FaceTime or through a secure call.
Security Keys, meanwhile, builds on Apple’s existing two-factor authentication system by requiring a hardware security key as one of the two factors to authenticate a person’s Apple ID credentials. Hardware keys come in a range of flavors and price points and typically use Bluetooth, NFC or USB to perform authentication.
Apple says that both iMessage Contact Key Verification and Security Keys for Apple ID will be available globally starting in 2023.
Apple launches end-to-end encryption for iCloud data by Kyle Wiggers originally published on TechCrunch